Technology Overview
Security as a design assumption, not an afterthought
At MobilWithUs, technology begins with a simple principle: security should not become an obstacle to innovation. We view security not as an add-on or a reactive measure, but as a fundamental design assumption.
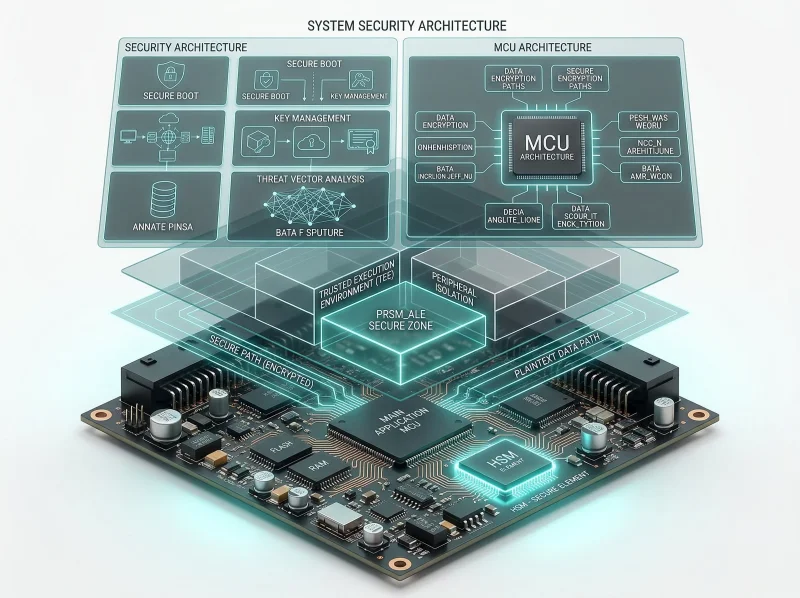
Embedded Security Architecture
MobilWithUs designs security architectures optimized for the structural characteristics of embedded systems such as controllers, ECUs, and industrial control units. By considering limited resources, real-time constraints, and long lifecycle requirements, we adopt lightweight and modular architectures.
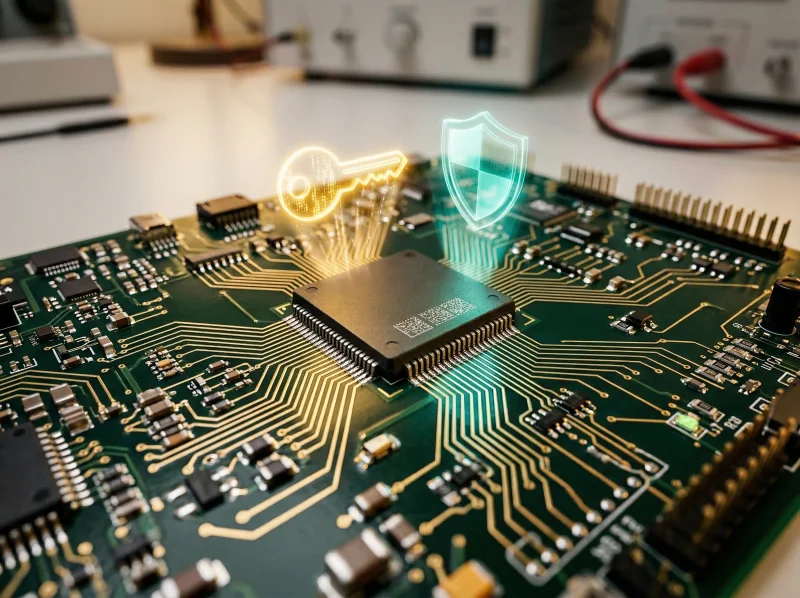
Hardware-backed Security
MobilWithUs leverages hardware security modules (HSM/HSE) as the core trust anchor of embedded security. By delegating cryptographic operations, key protection, and secure boot anchors to hardware, we achieve stronger security and higher reliability.
Secure Storage & Integrity
MobilWithUs designs secure storage architectures to protect sensitive assets such as keys, credentials, and security configurations. We also implement integrity verification at both boot-time and runtime.
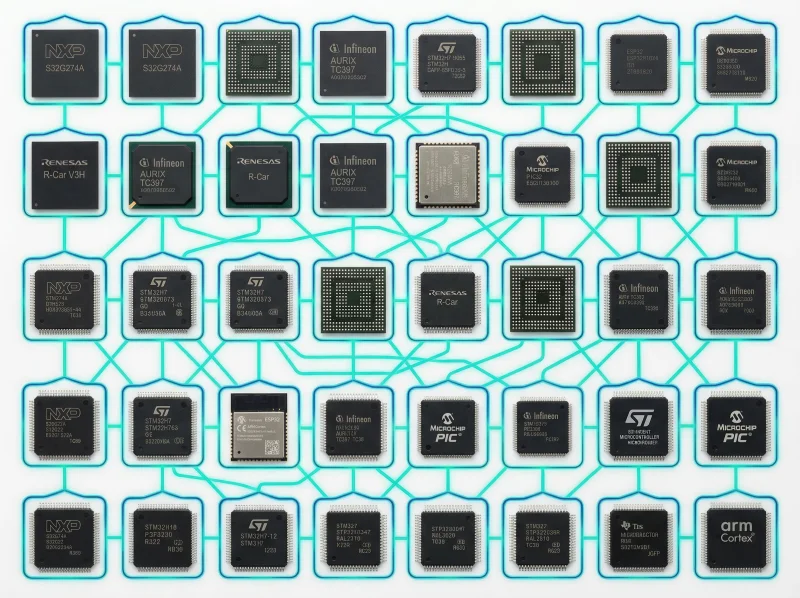
Multi-Core & Platform Experience
MobilWithUs has extensive experience implementing security across diverse MCU and SoC architectures. From single-core to multi-core environments, we design security with clear trust boundaries and role separation.
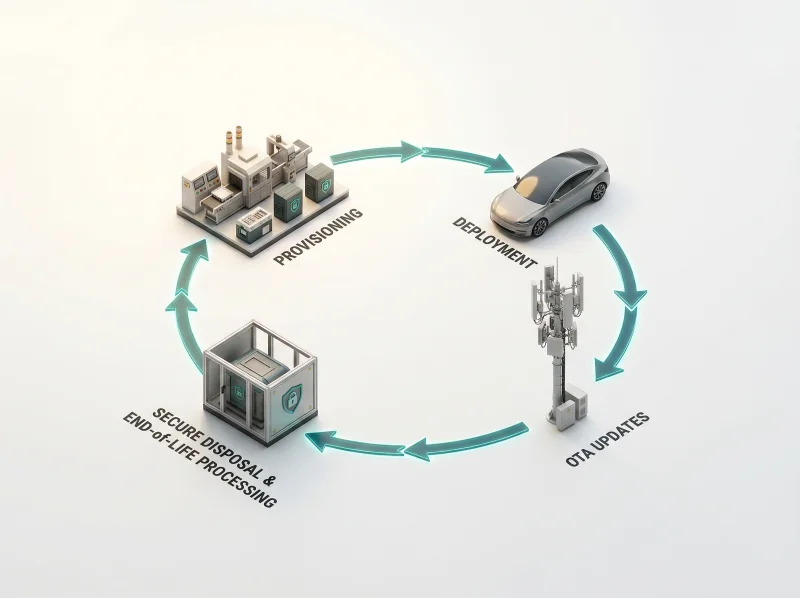
Security Lifecycle Management
Security does not end at deployment. MobilWithUs designs security management approaches that cover the entire system lifecycle — from provisioning and updates to patch management and decommissioning.
Conversation
What type of product? Deployment environment?
It's an embedded environment
UserAI identifies gaps through dialogue
Orchestration
AI automatically orchestrates the right tools
Deliverables
Audit-ready outputs generated instantly
AI & Regulatory Technology
Extending beyond embedded security into software supply chain security and regulatory compliance. Through AI agent orchestration, we automate SBOM generation, vulnerability analysis, and CRA/TARA compliance assessment — enabling organizations to start regulatory compliance through a conversational interface, without dedicated security experts.